But My WordPress Developer Said They Installed A Security Plug-in
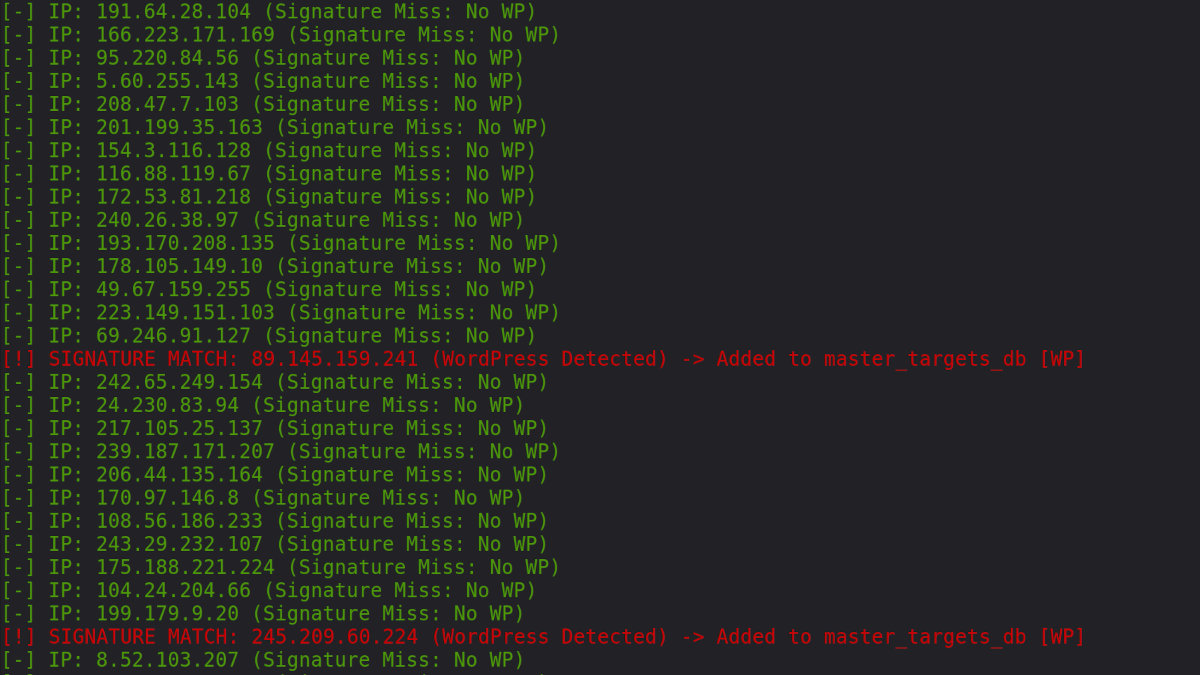
This is a Python script that will scan every IP address on the internet
*Note - I had someone look at this and recommend removing the code itself because it can be misused. They are wrong. Hiding how easy this is helps the dirtbags, not the business owners. I prefer education over ignorance.
import requests
import ipaddress
# The script targets the public internet, skipping private ranges
# like 10.0.0.0/8, 172.16.0.0/12, and 192.168.0.0/16
def scan_the_web(network_range):
for ip in ipaddress.IPv4Network(network_range):
if ip.is_private:
continue # Skip the internal stuff, focus on the targets
target_url = f"http://{ip}/wp-login.php"
try:
# Quick "handshake" to check for the WordPress fingerprint
check = requests.get(target_url, timeout=1, allow_redirects=False)
if check.status_code == 200:
print(f"[!] WordPress Identified: {ip}")
# Log to the database for the next exploit cycle
record_target(ip, "WP_Detected") # Writes the IP to a table
except requests.RequestException:
# Hardened servers or non-WP sites simply drop the connection
pass
# The bot runs this 24/7 across the global IP space
scan_the_web('0.0.0.0/0')
When paired with ZMap, a readily available package on Github, the scanning power is staggering. This very simple script will scan the entire internet, about 4 billion IP addresses, in about 45 minutes. It is designed to find every WordPress installation. If I were a dirtbag, I would create a very simple database table and store every one of those addresses for exploit.
Ok, You Have Every WordPress Install, Now What?
I know where I can find the latest exploits, for WordPress and most other systems. They are published just like a Substack subscription to anyone that wants to subscribe. You don't have to be a genius hacker to break into someone's systems, generally, you only have to be the first to hit the vulnerability.
I would get the latest exploit, and possibly use the script the real hacker has already created, and run it against my database filled with WordPress sites.
It Can't Be That Simple, Can It?
Yeah, it really is that easy. The only thing this takes now is just a little bit of knowledge. Years ago, it took quite a bit of expertise to break into a system. Now, it doesn't take much effort at all.
All you have to be is a dirtbag.
There are about 13,000 of these hacks happening a day, and once a vulnerability is discovered, mass exploitation happen within five hours.
Five hours, and 74% of all vulnerability attacks were not blocked, even by those expensive, up to date plug-ins you had installed.
And the number of exploitable vulnerabilities have doubled between 2023 and 2025.
Who can afford to keep up with that type of attack surface? People are gambling with their Digital Foundation.
What Can I Do?
Stop being such an easy target. WordPress powers an estimated 42% of the internet. That means it is the world's largest attack surface. When you use the same software as everyone else, you are a "known entity" to every bot on the planet.
The solution isn't another plugin.
The solution is Infrastructure.
It means starting from a different foundation, not bolting more software onto a known target.
I build custom systems on hardened, constantly updated, Linux environments. When that 45-minute scan hits one of my servers, it doesn't find /wp-login.php. It doesn't find a WordPress fingerprint. It finds a blank wall, gets bored, and moves on to the next easy target in a fraction of a millisecond.
My server gets hit thousands of times a day by these simple bots, and they hit brick walls or hear dead air.
Sources
WordPress Security Statistics 2025–2026: 43 Verified Data Points - Archive